'InstallFix' campaign exploits AI coding tools to spread malware via fake Claude sites
New 'InstallFix' campaign uses fake Claude AI sites and malvertising to trick developers into executing malicious code, exploiting trust in AI coding tools.
Security teams grapple with agentic AI Auto-Remediation readiness
Security teams face readiness challenges as agentic AI promises autonomous threat remediation, raising questions about trust, governance, and infrastructure preparedness.
AI-Powered attackers outpace patching: Bug exploitation now top Google cloud attack vector
AI empowers attackers to exploit cloud vulnerabilities faster than patching cycles, making bug exploitation the top Google Cloud attack vector, surpassing credential theft.
White house cyber strategy pivots to offensive operations: A new era of digital deterrence
Trump administration's 2018 National Cyber Strategy marked a historic shift toward offensive cyber operations, emphasizing preemption and deterrence over defense.
Xygeni GitHub action compromised via tag poison attack: Critical supply chain breach exposes enterprise security risks
Xygeni's GitHub Action fell victim to tag poisoning attack, allowing C2 implant to operate for a week, highlighting critical supply chain vulnerabilities.
How Ceros gives security teams visibility and control over Claude code AI agents
Ceros provides critical visibility and control over AI coding agents like Claude Code, addressing security gaps as these autonomous tools proliferate in enterprises
Tracking pixels exposed: How Meta and TikTok harvest user data beyond their platforms
Meta and TikTok use tracking pixels to harvest sensitive user data including credit card info and locations from external websites, extending surveillance beyond social platforms.
Unmasking Badbox 2.0: How Kimwolf gang's bragging revealed the android TV botnet operators
Kimwolf botnet operators accidentally exposed Badbox 2.0's Android TV streaming device botnet through bragging screenshots, giving FBI and Google new leads.
Meta's Instagram E2EE shutdown: A critical analysis of privacy implications
Meta's decision to end Instagram E2EE support by May 2026 marks a significant privacy retreat, affecting millions who rely on encrypted messaging for
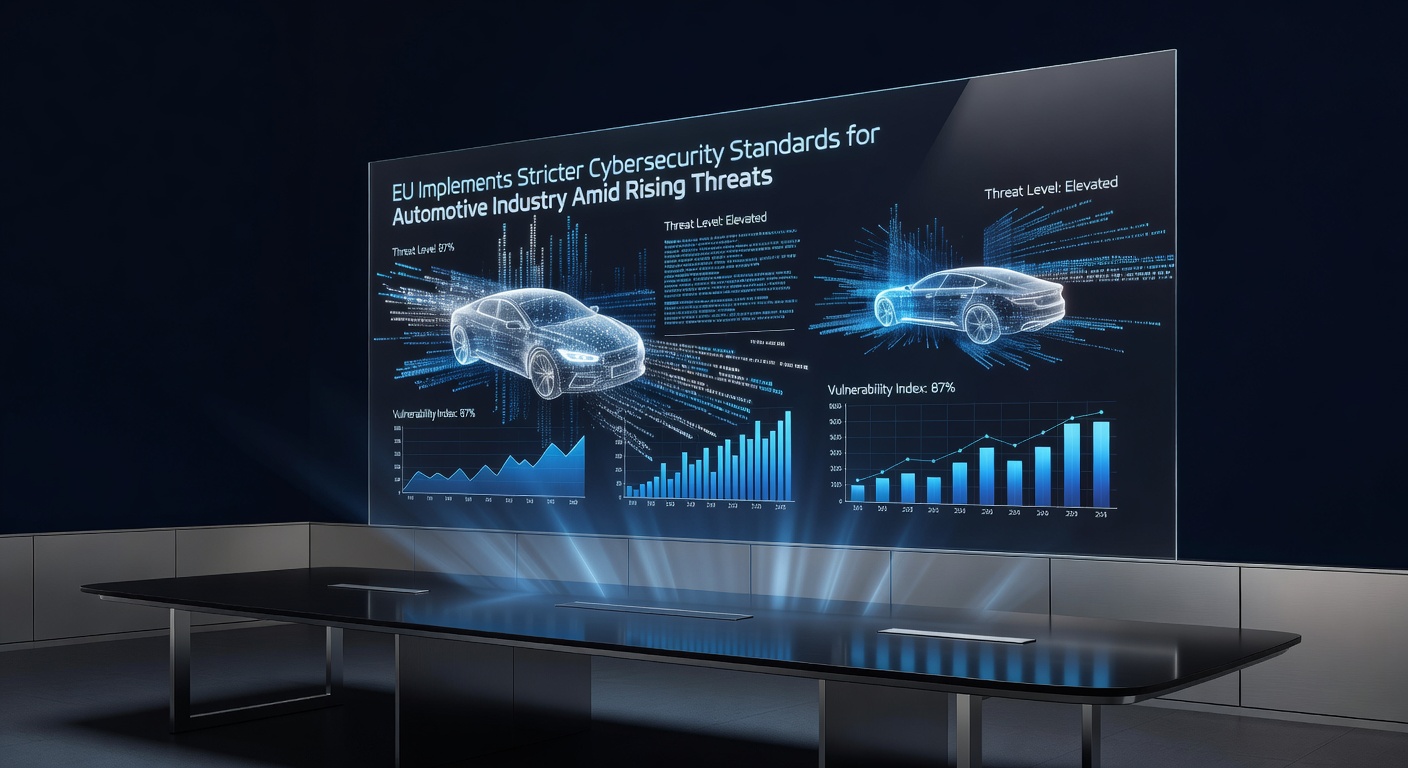
EU implements stricter cybersecurity standards for automotive industry amid rising threats
EU introduces mandatory cybersecurity standards for automotive industry, requiring comprehensive risk management as connected vehicles face increasing threats.
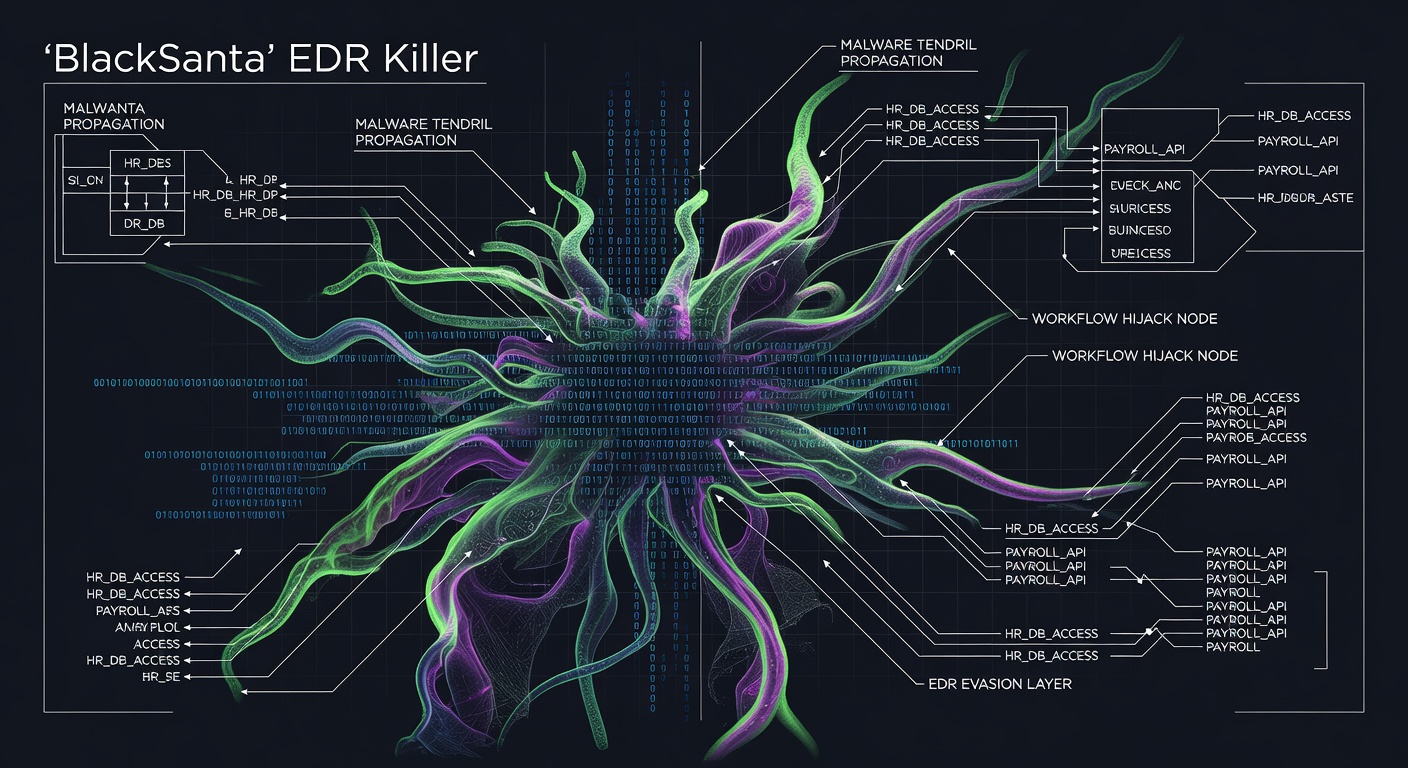
'BlackSanta' EDR killer hijacks HR workflows to evade detection
Russian cybercriminals deploy 'BlackSanta' malware through HR workflows, bypassing EDR security to steal data undetected in sophisticated new campaign.
Fig security emerges from stealth with End-to-End security operations monitoring platform
Fig Security launches from stealth with platform that monitors security data flows across SIEMs and response systems to prevent critical infrastructure breaks.