Why Stryker's outage is a disaster recovery wake-up call
Stryker’s outage shows why cyber resilience, not just compliance, now defines business continuity in regulated industries.
EU sanctions companies in china, Iran for cyberattacks
EU cyber sanctions on firms in China and Iran raise urgent supply chain, compliance, and vendor risk issues for businesses operating in Europe.
Russian hackers exploit Zimbra flaw in ukrainian government attacks
APT28 hackers linked to Russia’s GRU are exploiting a Zimbra flaw to target Ukrainian government entities, highlighting urgent patching needs.
Nation-State actor embraces AI malware assembly line
Pakistan-linked APT36 is using AI to mass-produce mediocre malware, shifting cyber risk from sophistication to scale and straining defenses.
54 EDR killers abuse 34 signed vulnerable drivers to blind security tools
Researchers found 54 EDR killers abusing 34 signed vulnerable drivers via BYOVD, exposing a growing kernel-level threat to enterprise defenses.
CISOs struggle to defend AI systems with outdated security tools, new study reveals
New study reveals majority of security leaders lack proper tools and skills to defend AI systems, creating critical vulnerabilities as organizations d
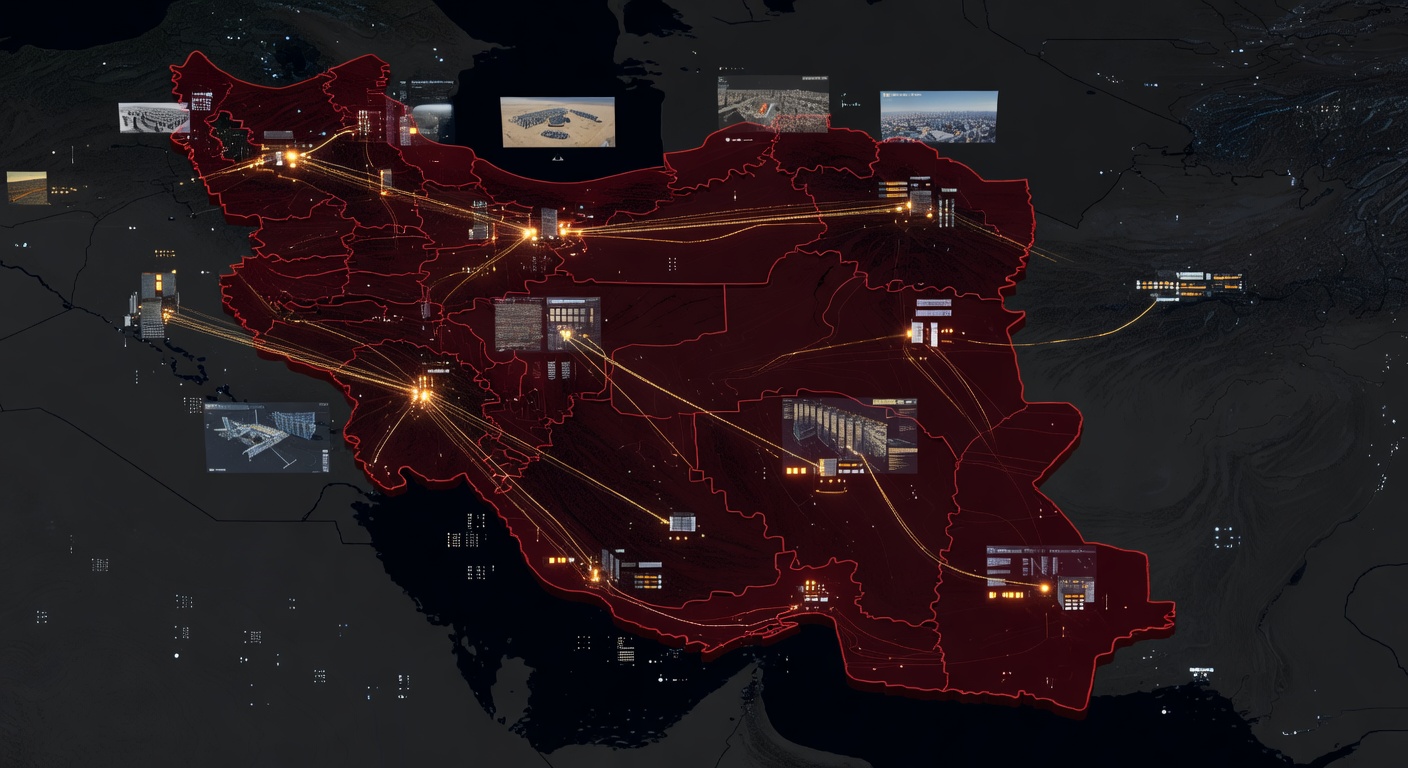
Iran's Pre-Positioned cyber arsenal: Six-Month infrastructure buildup reveals new threat model
Iranian state actors spent six months building resilient cyber infrastructure using US shell companies, designed to survive military retaliation durin
Iran-Backed hackers target medical giant Stryker with devastating wiper attack
Iran-backed hackers deploy destructive wiper malware against medical giant Stryker, forcing evacuation of 5,000 Irish workers and threatening global h
AI-Powered cyberattack on Mexican government agencies exposes new era of sophisticated threats
Mexican government agencies fell victim to AI-powered cyberattacks using ChatGPT and Claude, exposing citizen data and highlighting new era of AI-enabled threats.
Nordstrom's email system exploited in sophisticated cryptocurrency scam campaign
Cybercriminals exploited Nordstrom's legitimate email infrastructure to send cryptocurrency scam messages disguised as St. Patrick's Day promotions.
North korean apts weaponize AI to supercharge IT worker infiltration scams
North Korean APTs are using AI tools like deepfakes and automated communications to enhance IT worker infiltration scams, making them harder to detect.
Tycoon 2FA phishing empire crumbles: Europol takes down MFA-Bypassing criminal platform
International law enforcement dismantles Tycoon 2FA, a sophisticated phishing platform that helped cybercriminals bypass multi-factor authentication protections.